http://www.newscientist.com/blog/technology/2007/04/seeing-through-walls.html
Technology
A technology blog from NewScientistBlogs
Friday, April 20, 2007
Seeing through walls 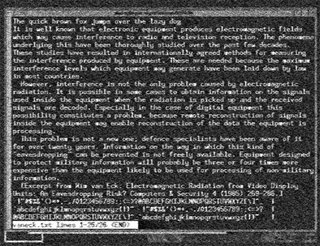 Have
you considered that someone could be reading what's on your monitor from a few
rooms away? It's unlikely, but possible, as work by Cambridge University
computer security researcher Markus
Kuhn shows.
Have
you considered that someone could be reading what's on your monitor from a few
rooms away? It's unlikely, but possible, as work by Cambridge University
computer security researcher Markus
Kuhn shows.
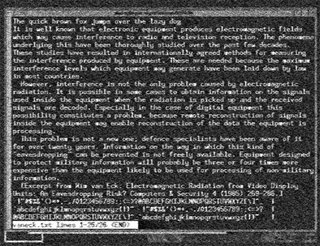
A radio antenna and radio receiver - equipment totalling less than £1000 - is
all you need. Kuhn managed to grab the image to the left through two
intermediate offices and three plasterboard walls.
Back in 1985, Wim Van Eck proved it was possible to tune into the radio
emissions produced by electromagentic coils in a CRT display and then
reconstruct the image. The practice became known as Van Eck Phreaking, and NATO
spent a fortune making its systems invulnerable to it. It was a major part of
Neal Stephenson's novel Cryptonomicon.
CRTs are now well on the way to being history. But Kuhn has shown that
eavesdropping is possible on flat panel displays too. It works slightly
differently. With a flat panel display the aim is to tune into the radio
emissions produced by the cables sending a signal to the monitor. The on-screen
image is fed through the cable one pixel at a time. Because they come through
in order you just have to stack them up. And Kuhn has worked out how to decode
the colour of each pixel from its particular wave form.
If everything is just right, you can pick up signals from some distance.
"I was able to eavesdrop certain laptops through three walls," says
Kuhn. "At the CEBIT conference, in 2006, I was able to see the Powerpoint
presentation from a stand 25 metres away." Here's the image he managed to
get:
 Kuhn
also mentioned that one laptop was vulnerable because it had metal hinges that
carried the signal of the display cable. I asked if you could alter a device to
make it easier to spy on. "There are a lot of innocuous modifications you
can make to maximise the chance of getting a good signal," he told me. For
example, adding small pieces of wire or cable to a display could make a big
difference.
Kuhn
also mentioned that one laptop was vulnerable because it had metal hinges that
carried the signal of the display cable. I asked if you could alter a device to
make it easier to spy on. "There are a lot of innocuous modifications you
can make to maximise the chance of getting a good signal," he told me. For
example, adding small pieces of wire or cable to a display could make a big
difference.
As for defending against this kind of attack, Kuhn says using well-shielded
cables, certain combinations of colours and making everything a little fuzzy
all work.
For another cool security demonstration by Kuhn, check out this story on decoding
the flicker a monitor casts on the walls.
Tom Simonite - online technology reporter.
Labels: displays, eavesdropping, hacks,
security
- Posted by Tom at 6:59 PM
- Permalink
- del.icio.us
- digg
this
 Have
you considered that someone could be reading what's on your monitor from a few
rooms away? It's unlikely, but possible, as work by Cambridge University
computer security researcher Markus
Kuhn shows.
Have
you considered that someone could be reading what's on your monitor from a few
rooms away? It's unlikely, but possible, as work by Cambridge University
computer security researcher Markus
Kuhn shows.
A radio antenna and radio receiver - equipment totalling less than £1000 - is
all you need. Kuhn managed to grab the image to the left through two
intermediate offices and three plasterboard walls.
Back in 1985, Wim Van Eck proved it was possible to tune into the radio
emissions produced by electromagentic coils in a CRT display and then
reconstruct the image. The practice became known as Van Eck Phreaking, and NATO
spent a fortune making its systems invulnerable to it. It was a major part of
Neal Stephenson's novel Cryptonomicon.
CRTs are now well on the way to being history. But Kuhn has shown that
eavesdropping is possible on flat panel displays too. It works slightly
differently. With a flat panel display the aim is to tune into the radio
emissions produced by the cables sending a signal to the monitor. The on-screen
image is fed through the cable one pixel at a time. Because they come through
in order you just have to stack them up. And Kuhn has worked out how to decode
the colour of each pixel from its particular wave form.
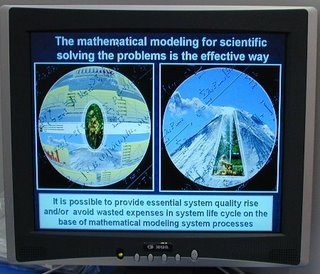
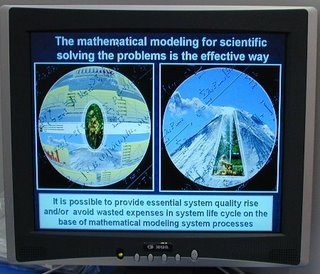
If everything is just right, you can pick up signals from some distance.
"I was able to eavesdrop certain laptops through three walls," says
Kuhn. "At the CEBIT conference, in 2006, I was able to see the Powerpoint
presentation from a stand 25 metres away." Here's the image he managed to
get:
 Kuhn
also mentioned that one laptop was vulnerable because it had metal hinges that
carried the signal of the display cable. I asked if you could alter a device to
make it easier to spy on. "There are a lot of innocuous modifications you
can make to maximise the chance of getting a good signal," he told me. For
example, adding small pieces of wire or cable to a display could make a big
difference.
Kuhn
also mentioned that one laptop was vulnerable because it had metal hinges that
carried the signal of the display cable. I asked if you could alter a device to
make it easier to spy on. "There are a lot of innocuous modifications you
can make to maximise the chance of getting a good signal," he told me. For
example, adding small pieces of wire or cable to a display could make a big
difference.
As for defending against this kind of attack, Kuhn says using well-shielded
cables, certain combinations of colours and making everything a little fuzzy
all work.
For another cool security demonstration by Kuhn, check out this story on decoding
the flicker a monitor casts on the walls.
Tom Simonite - online technology reporter.
Labels: displays, eavesdropping, hacks,
security
- Posted by Tom at 6:59 PM
- Permalink
- del.icio.us
- digg
this
All comments should respect the New Scientist House Rules. If you think a particular comment breaks these rules then please let us know, quoting the comment in question.
This is interesting.
I would like to know more.
Jim Somchai
http://www.visualizationmeditation.com/rights
By on April 20, 2007 7:27 PM
I have never been to CBIT, but that bottom slide... Written by an 'executive' maybe?
And, he caught an image that managed to include the bezel? Or, he caught an image on his computer, and to show everyone, he photographed it with a digital camera?
Did the reporter loose the pic and substitute some nonsense clip art? Whats going on here?
By Martin on April 21, 2007 9:20 AM
My favorite of the proposed solutions is the last one; 'making everything a little fuzzy'. I haven't used it, but if Vista has a Gaussian blur effect for some of its UI, Maybe they should issue a security patch and apply that effect over the whole screen.
If you want to read more about the subject, have a look at the introductory article Eavesdropping attacks on computer displays, the paper Electromagnetic eavesdropping risks of flat-panel displays (2004 Workshop on Privacy Enhancing Technologies), or for all the gory details my thesis Compromising emanations: eavesdropping risks of computer displays.